Cryptocurrency Investing
What is 2FA & How Two-Factor Authentication Security Works

What is 2Factor Authentication? (2FA)
Despite popular belief, the biggest threat that stands between you and your cryptocurrency investment portfolio is not its volatility, but the security of the funds you have. Although most of the smart learners today have moved across to hardware wallets such as the Ledger Nano S for securing cryptocurrencies, most of us rely on exchanges to keep our money safe.
It’s certainly not the best practice, yet that is usually the best course of action, as managing an individual wallet for each coin you have is highly impractical. Although the prospect of top crypto exchanges shutting down is a realistic threat, this is the least of your worries. What you should worry about is getting hacked due to your lack of security practices.
If you need more reasons for why this is the case, then read head. According to the site Chainalysis, cyber thieves have taken more than $225 million dollars ‘worth of Ethereum in 2017, using a website phishing attack. This means that criminals today need to do nothing more than to clone or poof a legitimate website to steal your details.
Also, Bloomberg has highlighted the fact that there is a 1 in 10 chance that you will get your money stolen whilst investing in an ICO.
All of this leads to one obvious conclusion: that there is a critical need for each person to be far more diligent whilst investing in cryptocurrencies and make cybersecurity an additional priority.
So how can we begin to do that? Let’s start with securing your account from intruders, which is where Two Factor Authentication (2FA) comes in. 2FA is one of the easiest and most powerful ways that you can secure your account. It takes minutes to setup, and while imperfect, it goes a very long way to keeping your coins secure.
Let’s quickly go over what 2FA is and how you can set it up on your computer.
What is Two Factor Authentication (2FA)?
As you could probably figure out already, 2FA adds an additional layer of security for your trading account. Unfortunately, the standard security methods used today with many applications are simply not up to standards, which means that your information can easily be taken away from you. In fact, it’s scary how easy it is now for cybercriminals to get their hands on your account’s information and password. In this case, 2FA helps to ward of criminals so that they cannot log in to your account, even if they know your password.
How Does 2FA Work?
How does 2FA do this? By ensuring that each login that is made to your account is made by only one person: you. Here are some factors that usually come bundled with your login credentials:
- Something you know: This could be a combination of passwords, PIN, or a ‘secret question’ that only you have the answer to.
- Something you have: This could be a code, USB dongle, or something sent to an email address that is under your control.
- Something you are: These are things that relate to your human body, such as a fingerprint, retinal scanner, or voice.
Example of 2FA
Two-factor authentication can be implemented in various ways. Let’s take a glance at an actual example to understand the concept. Afterwards, we will explain how you can use 2 factor authentication in your crypto portfolio to make your coins less likely to be hacked.
Traditional use of 2FA
Let’s say that you have a safe inside a bank where you save all your belongings. The bank dispenses the key for the lockers to their customers. However, to access the safe, two keys are required: one form the customers and another from the bank. This is the essence of two factor authentication.
Alternatively, your debt card and ATM pin are both examples of 2FA since you can’t use one without the other.
How Does 2FA Work?
Two factor authentication works in the same way as your existing login process. The only difference is that you need to enter an extra piece of information in concert with your ID and password.
This extra information can be transmitted to you through the means of a onetime password (OTP) that is posted to your mobile number or email address. This can take the form of a code on an application such as the Google Authenticator or Authy that you need to enter on the website’s login, along with your username and password.
Using your email account or SMS to verify your identity is not the safest way, as it leads your account to being compromised by hackers. It’s a fact that it’s easier to be hacked via social engineering using these methods, which can allow them to get access to your sim card. However, when we use a mobile application for making this token, it puts you in a place of complete control of your account’s security. If you have not used 2FA before, then you should start using it now. It’s simple to setup and it strengthens your account’s security.
Benefits of Two Factor Authentication (2FA)
Here are some popular reasons for why you should be using 2FA on your account right away.
Enhanced Security
2FA adds an additional layer of security to your trading account that is much needed. This means that even if your account were to be hacked by someone who has your username and password, they will need an additional piece of information to withdraw funds from your trading account. These hacks are not uncommon, and they will likely increase in frequency as cryptocurrencies become more popular.
So, since hackers are not likely to have access to your mobile phone or email address, this feature if what allows 2FA to be so attractive for users who want to increase the security of their trading accounts. This principle holds true even for brute force attacks, which is when a piece of software is used to guess your password by going through a countless number of guesses.
Improved Accessibility
With an increased feeling of security, users and management do not need to organize a secure office environment to access sensitive information. This can be now be accessed while on the move with two factor authentication acting as a barrier for mobile tech.
Therefore, employees can now get access to company information such as data, documents, worksheets and more via any virtual device. All this today is now done without putting the safety of sensitive information in danger, as well as keeping it secure always.
For example, if an employee uses their personal tablet to log in to a company website, no other person can access the information after the session is over, since 2FA makes this impossible without access to the username and password.
Lower Costs
Due to the threats of coordinated attacks from criminals, cybersecurity at the corporate level is a priority today. This has led companies to handle this matter urgently and adopt the best practices that they can to keep their data safe.
But the expenses associated with these security practices are high.
This is another benefit of 2FA, as it provides a simple and easy way for organizations to manage their security problems. This is especially true for small companies and startups who are constantly on the lookout to save time and money.
Customers Query Management
Another issue that companies face is the handling of customer questions relating to their logins. This usually takes the form of tickets and a helpdesk process, which takes up a lot of time for the company if it is not automated.
With two factor authentication, it is possible to take away this inefficiency by letting the user reset their own passwords through using a combination of their email and the authentication method they have chosen.
What’s more is that it can also stop hackers from taking advantage of the ‘Reset Password’ system to gain access to your account.
Stops Identity Theft
You can stand to lose a lot in case a hacker gets access of your account. Identity is one of the key first world crimes that we are facing today. The Identity Fraud Study that was conducted in 2017 revealed that $16 billion dollars was stolen from 15 million people in the United States alone.
These kinds of crimes are possible since once a hacker has control over your account, all the other accounts and sensitive information will also be available to them. For example, if your cryptocurrency account is hacked today, your linked banked account along with your KYC will also be up for grabs.
This means that 2FA could be your best option for protect against these attacks.
The most up to date way to secure your account using 2FA is using a hardware device such as YubiKey. However, most of us will use an application such as the Google authenticator or Authy to use 2FA when you use major exchanges such as Binance or Bittrex, you will be used an app-based 2FA method.
Before we go into details of how to use the Google authenticator for 2FA, let’s check how YubiKey measures up. Soon, you should plan to move your 2FA method to a more secure piece of hardware.
How to use Yubi Key
If you are ready to jump on board with 2FA and looking for an easy tool to help you do this, then YubiKey could be the solution that you have been looking for.
For starters, YubiKey is a hardware authentication dongle that is packed with a range of features such as one-time passwords, authenticators, encryption, and the 2nd Factor protocol
If the above information has been convincing enough and you are already looking for an effective tool to set up 2FA, one noteworthy mention here is YubiKey.
This means that it can function as a secondary authentication factor, or something that the user has that allows them to login securely to their accounts. OTP will give you a private and public key pair that is made by Yubi. Yet the best feature of Yubi is that it can be used with any website, even those that do not support OTP. This is facilitated through the help of static passwords.
The integrity of the device can be verified by the fact that both Facebook and Google use it.
And if you are on the hunt for a 2FA application, you can use either the Google authenticator or Authy.
Both tools work through the inclusion of a random string of numbers for accounts for website where you can use 2FA to interface between them. This adds some much-needed swiftness to the whole process for easy logins.
Authy differs quite a bit from the Google Authenticator in several ways. First, Authy requires your phone number as well as your email address. Your phone number is used to send a verification pin that is needed when setting up your account. Second, Authy provides multi-device support, while Google does not.
This is important, as what would happen if your device was stolen and you had all your 2FA information set up through the Authenticator application? There would be no way to get that information back.
So, with Authy, you can take away all the 2FA credentials from your lost or stolen devices and authorize a new device for each of your accounts. Also, the application is available for all devices, not only mobile phones.
Despite these advantages, most people use the Google Authenticator as it is made by Google and its security is one of the best in the industry. You can even use the Google Authenticator to verify your logins with the most popular crypto exchanges, which is something that we will go into detail with in another guide.
Two-Factor Authentication Security Summary
To put it simply, this is how you can set up 2FA on your exchange accounts to add an additional layer of security for your logins. It would be foolish to overlook the security of your account in today’s world of cybercrime and major hacks.
Remember that are at any point in time, you alone are responsible for your own security, and you will only have yourself to blame if something goes wrong!
Cryptocurrency Investing
MetaMask: Ethereum ERC20 Token Wallet Browser Extension Beginner’s Guide
The Beginner’s Guide to MetaMask
For those new to Ethereum or perhaps even cryptocurrencies in general, the name MetaMask has probably already popped up in conversations. MetaMask is essentially a browser extension, and acts both as a wallet and access point to the Ethereum network. Explained even simpler, MetaMask is a hot wallet.
On the blockchain cryptocurrency networks, users can opt for a hot wallet (“live” or actively connected to the network) or a cold wallet (disconnected from the network). A wallet is necessary to store personal altcoins off exchanges or anywhere else after trading or transacting.
Although many early exchanges act as a bank for digital traders, current wisdom dictates that users maintain their funds offsite. In addition, a user will very often need to fund a trading account from a wallet, as many don’t allow for fiat or legacy payment protocols.
There are pros and cons to both, and current trends see most users employing the duo as their needs dictate. A hot wallet can be accessed and pilfered through phishing or user error, whereas a cold wallet is dead to the network, allowing no access at all. A cold wallet is also sometimes called a vault, as it’s silent, secure and access-restricted.
Many users will encounter the name when looking at ICOs, because ICOs are dominated by the ERC-20 token protocol. ERC-20 is a “type” of token, developed and employed on the Ethereum network, that has proven the most malleable and compatible token structure for crowdfunding purposes. The vast majority of ICOs, while employing their “own” tokens, are actually building those tokens out of the ERC-20 protocol.
MetaMask Details
Looking at a few nuances of the wallet, since it is an organic build from the Ethereum network, the MetaMask wallet will only hold ETH coins and other ERC-20 tokens of whatever origin. Bitcoin, for example, cannot be held in a MetaMask wallet.
The other major component of MetaMask is that it is a gateway to the Ethereum network. What this means is that all of the network’s dapps are available to use for MetaMask wallet holders. Dapps are “decentralized apps” and so named because their backend code is running on a decentralized network, in this case the Ethereum network.
If dapps seem obscure, examples would be the game Cryptokitties or casinos like Etheroll, a marketplace like OpenSea and of course digital exchanges like ForkDelta and IDEX.
Without a middleman like MetaMask, a PC’s browser can’t access the Ethereum network. Not unless a user runs a “full node” and installs the whole 400GB Ethereum blockchain on their PC.
The reason why MetaMask is known as a browser extension is because MetaMask injects a javascript library in your browser page. The javascript is called web3.js and written by the Ethereum development team.
Installation and Setup Of MetaMask
MetaMask is “open source,” which means anyone can view the code on GitHub. Currently, MetaMask functions on the FireFox, Chrome, Brave and Opera browsers. Links to MetaMask extensions for all relevant browsers are readily available on the MetaMask homepage. Once installed, the MetaMask logo will appear in the top right of the screen. Chrome, for one, will typically ask you to enable an extension, but these steps are all linked and users are done with a MetaMask installation in a minute or two.
Users don’t require a username when registering a MetaMask wallet, only a password. With MetaMask, a user’s password is called a “DEN.” although a clever play on words, since the logo is a fox’s face, although this appears to be more coincidence than any deliberate naming.
After creating a password, users are issued with a unique 12-word “seed phrase.” This is a bunch of words employed to safeguard a user’s account. It’s recommended that users stash their seed words in a competent password keeper like LastPass, or similar apps. Users can also generate multiple MetaMask accounts. Every account created by a user with MetaMask will share seed words and the password, but will have a different address.
Transacting With MetaMask
Paying someone or otherwise dispatching tokens from the MetaMask wallet is a simple matter. A single click on “Send” allows users to populate the subsequent screen with a user address. Send the funds and the transaction is done, and users receive a confirmation once the transaction is completed.
When interacting with dapps using MetaMask, provided a user is logged into their MetaMask account, they can access Ethereum network dapps automatically through their browser. Logging into a dapp like OpenSea, for example, the decentralized outlet for crypto collectibles, the dapp notes a user’s MetaMask address. There is no need to log into dapps separately, as the network has user intel integrated, recognizing an account holder wherever they go on the Ethereum blockchain.
MetaMask is free to use, users paying only the “gas” cost – the base cost of transacting on the Ethereum network. Gas is the fee required to effect any transaction on the Ethereum network. It is denominated in “Gwei,” one billionth of an ETH. Looking at overall UX, MetaMask is a reputable offering, with good support and a welcome absence of any dark press.
Protecting Your MetaMask Account

How Safe is MetaMask? In the world of cryptocurrencies, security is top of the list. Constant hacks and successful phishing attempts keep making the papers, while legislators are still battling to bring regulation up to the same level as legacy fintech. Since cryptocurrency thefts cannot be undone by identifying the thief and reclaiming funds, users should always have security uppermost in their minds when employing their MetaMask wallet.
It is advised to log out of a MetaMask account when it’s not being used. When a user is logged in, the account is considered “unlocked” and more vulnerable than when shut down. Open MetaMask accounts enable crooks to glean a user’s wallet address, token types, the wallet balance and especially transaction history.
Don’t be fooled into thinking that phishing can only happen via mail, however. Users should be aware of suspicious pop-ups or other notifications while signed into their wallet, as this can also be indicative of a phishing attempt.
Things like irregular pop-ups that ask a user to sign for a pending transactions are high risk. So too are messages telling users that their last transaction failed, then rerouting the repeat transaction to a different address. Much like cyber criminals emulate bank UIs and present with all the right logos and all the right colors in place, so too have there been instances of phony interfaces emerging.
For the best secure arrangement, users would employ a cold wallet like Ledger or Trezor Model T. For human reassurance, keeping the bulk of one’s altcoin holdings in a cold wallet can’t be beaten. That said, MetaMask has never suffered a hack nor had other instances of bad, sad press around lost funds and theft. To date, the wallet is impervious, and user losses stem from phishing attacks for which MetaMask can’t be blamed.
MetaMask Conclusion

MetaMask is elegantly simple and easy to use. The wallet-stroke-network enabler has become the most popular and convenient route to navigating, paying and trading on the Ethereum network. Standing back and looking at the offer as a non-technical or, rather, non-crypto person might, as an offer it’s very simple and easy to install.
Even newcomers can quickly grasp the essence of it and get on with interacting on the Ethereum blockchain. MetaMask is intuitive and has been elegantly simplified because of its homegrown Ethereum nature. Any hot wallet, however, carries a higher risk than any cold wallet, and users should always have caution in mind when transacting via the wallet.
You can read more about MetaMask here: metamask.io
Cryptocurrency Investing
Top 6 Cryptocurrency Exchanges Using Own Coins For Reduced Fees

Best Cryptocurrency Coins Which Grant Dividend Or Reduced Fees In 2018
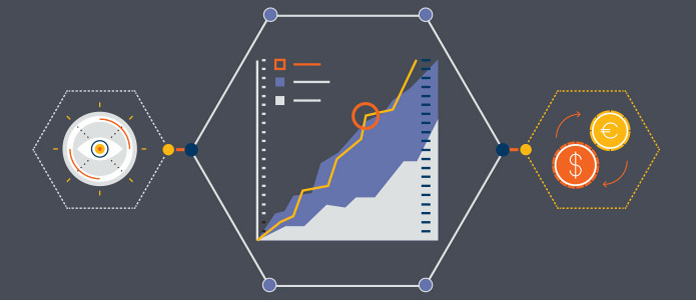
The cryptocurrency space has gained incredible momentum in the last few months. This is fueled especially by the existence of coins that not only earn dividends for the owners but also earn passive income while at the same time offering very low transaction fees.
Table Of Contents
6 cryptocurrency exchange coins and tokens that make money in the Crypto sphere are discussed below in detail.
KCS is a native token owned by KuCoin Cryptocurrency Exchange which is based out of Hong Kong. A total of 100 Million tokens of KCS were distributed during the KuCoin Initial Coin Offering (ICO) in 2017. KCS tokens are fundamentally ERC 20 tokens. The current value per token of KCS is US$ 4.78 and the market capitalization is approximately US$ 435 Million.
Holding KCS tokens is extremely advantageous for both Holders and traders. KuCoin Shares have a reward ratio for the holders. 10% goes to KuCoin, 50% goes to the KCS holder and 40% belongs to the referred individual. 10% of the Exchange`s profits are used in buying back the KCS and then burning the tokens. This means that KCS holders are further rewarded due to the appreciating prices.
Furthermore, Owners of KCS receive 50% reduction of the platform`s trading fees on all the volumes in the Exchange. Due to the referral system at the KuCoin Cryptocurrency Exchange, owners of KCS receive higher passive income.

Binance (BNB) Token
BNB is a native coin that is owned by Binance, which is one of the best cryptocurrency exchanges in the current Crypto market. Binance exchange was developed in China but relocated to Japan in September 2017. BNB has a current market value of US$ 11.82 and a market capitalization of US$ 1.3 Billion.
BNB is also an ERC 20 token with a fixed supply of 200 Million. During the Initial Coin Offering (ICO) in 2017, the BNB token was generated to fund the development of Binance Exchange. Owners of BNB token use it to pay for fees on the Exchange`s platform. These fees include withdrawal fees, Listing fees, Exchange fees and any other applicable fees.
Binance buys back 20% of BNB tokens in every quarter which the Exchange then burns until the total circulation reaches 100 Million. For holders of BNB, the total cost of trading at the platform is reduced by 50%. The owners of BNB also receive regular dividends when the BNB tokens are regularly burnt every quarter till the total supply goes back to 100 Million. The increased daily volumes at the Exchange further increase the benefits by providing an increased passive income.

CryptoBridge (BCO) Coin
BCO is a native crypt-compatible coin created in July 2017. It is owned by the Decentralized Cryptocurrency Exchange (DEX) called CryptoBridge Dex which allows trading of most of the popular Altcoins. This Exchange utilizes the multi-signature federated gateway.
BCO coin is mineble and unlike KCS and BNB, it is not an ERC20 coin. BCO Coin has a current market value of US$ 1.64 and a market capitalization of US$ 45Million. Holders of BCO get 50% of the share bonus earnings of CryptoBridge Exchange when they stake their BCO coins.
For 3 months they receive 20% bonus, for 6 months they receive 50% bonus and for 12 months they receive 100% bonus. However, staking their coins for 1 month yields 0% bonus.
COSS Token
COSS is an ERC20 token that is owned by COSS Cryptocurrency Exchange located in Singapore. COSS exchange has matching features like Binance and KuCoin Exchanges. The Exchange is unique since it embraces plans of being a USD Exchange as well as payment processor.
The current market value of the COSS token is US$ 0.29 with a market capitalization of US$ 23 Million. The COSS Exchange retains and validates all the transactions that are initiated at the platform on the Ethereum Blockchain.
COSS has a great dividend program. The holders of the coin are paid 50% of the total earnings from the Exchange trading fees on a weekly basis. Additionally, holders can store their coins at the COSS Exchange platform or at an ERC20 enabled wallet such as MyEtherWallet.
CEFS token is another dividend earning token that is owned by the Cryptopia Exchange which is one of the most popular digital Exchanges trading numerous Altcoins. Cryptopia is headquartered in New Zealand.
CryptopiaFeesShares are very expensive and rare. The current market value is US$ 1,816 per token with a total supply of 6300 CEFS. The Cryptopia mining platform for cryptocurrencies is well streamlined and easy to use.
The holders of CEFS Token receive 4.5% of the monthly earnings from Cryptopia platform which is then distributed proportionately as per the CEFS holdings. Holding the token for longer periods leads to more returns.
Bibox (BIX) Token
BIX is a native token that is owned by the Bibox Exchange, an all enhanced-encrypted Exchange which was founded in China. It also has similar features like Binance. This exchange enables traders to trade numerous Altcoins. The exchange supports different languages like English, Chinese, Korean, Mandarin, Vietnamese and Russian. The Exchange is also unique since it has the capacity to trade cryptocurrencies while utilizing Fiat currency within the same medium.
The current market value of BIX is US$ 0.6 with a market capitalization of US$ 63M and a circulating supply of 105,918,066 BIX. The tokens are bought back and burnt regularly until the total supply reaches 271 Million.
Holders of BIX receive rewards in the form of fee reduction. BIX tokens have various uses especially in paying for the Exchange`s fees like Exchange fees, Listing fees and Withdrawal fees. The discount rates for using BIX are as follows: 50% in year one, 25% in year two, 12.5% in year three, 6.25% in year four and 0% in year five.
Our Final Thoughts
Conclusively, the best coin or token depends on the goal of an individual. For instance, an individual who is actively involved in trading is better suited to possess the BNB token while an individual whose purpose is passive income, then KCS is ideal. High volumes of the trading Exchanges will mean more dividends while the costs in trading and the referral systems will mean more passive income.
Cryptocurrency Investing
Top 5 Most Common Bitcoin & Cryptocurrency Scams in 2018

Cryptocurrencies have become a bit of hot cake. On one hand, lots of people are getting in and making a lot of money. Others are getting burned and losing their life savings in a bid to play in the markets and make a killing.
Most of those who do often invest in cryptos known as scam coins. These cryptocurrencies are designed to rip off people, and solely benefit their creators.
But because most newbies have no idea of how to identify the real moneymakers from the scams, many get burned, losing a lot of money in the process. This article is contains information on the more common cryptocurrency scams, show you how to identify them, and more importantly, teach you how to protect yourself, so you don’t get ripped off.
Types Of Cryptocurrency Scams
1. Cloud Mining Pools

Please understand that there are some legitimate cloud mining services out there. So, not all of them are bad. That said, this is one of the more common ways people lose their money.
These companies attract people who want to go into cryptocurrency mining, but have neither the time nor the money to buy and maintain their own cryptocurrency miners. So, these companies offer to help them mine, in exchange for a fee and a promise of the profits.
To identify the legit operations from the fraudulent ones, look for their registrants, company team lead and location. A major red flag is if you cannot find direct details when you do a whois lookup of their domain name.
But that alone isn’t enough. Look for transparency in terms of who runs what. Legitimate cloud mining services will have either their whois details available and/or information on the team managing the service.
Also be wary of companies registered in the US or UK, but with all team members resident abroad. If you cannot find a local address that’s verifiable, you might want to keep your money as that’s another red flag.
2. MLM Cryptocurrency Organizations

These are popping up all over the place and promising to make people instant millionaires. All participants have to do is get more people on board to invest in a specific cryptocurrency or a proxy project and they’ll profit from it.
The reality is that while there are legit multilevel marketing schemes, many of these crypto based MLM programs have no tangible product or service to sell. If the only thing they’re selling is a pyramid scheme, run and don’t look back.
3. Bogus Initial Coin Offerings (ICOs)

More and more people are realizing that they can make a lot of money from initial coin offerings. These people are taking advantage of the unregulated nature of the crypto space and the ease of creating tokens to launch ICOs.
In fact, it is estimated that over $1 billion has been invested in ICOs in the last 6-12 months, with many being unrealistic or downright fraudulent.
Unfortunately, many of these scammers are becoming more savvy and cleaning up their act by presenting a legitimate front –often with roadmaps, white papers, detailed information about their “projects” and other trappings that make their campaigns look legit. So, while it’s getting more difficult to spot the fake ICOs, it’s not impossible.
For starters, research thee company itself. If it’s been in business and has a good reputation, then you have a winner. If it’s new, has no reputation, and isn’t transparent about its processes, team or location, close that tab and keep looking.
Also, look at their management team and research them. Always go for those with well known and reputable team members. And if their promise or project sounds too good to be true, chances are it is.
4. Crypto Investment Packages

These are primarily bitcoin based and more formally known as bitcoin investment packages (BIPs). These are similar to cloud mining in the sense that they promise daily returns which are usually smaller percentages of your investment.
They often start out well to gain your trust, and then one day, disappear. This is another pyramid scheme designed to fleece you of your hard earned money. Users tend to fall for it by reinvesting their funds only to have their returns and payments gradually slow down and stop coming in altogether.
For these packages, we’ll say just walk away completely. And if you want to do this, just understand that it’s a short term Ponzi scheme and go in with your eyes open. For best results, get in at the very early stage, make your money, and cash out.
5. Pump and Dumps

These are projects created by individuals or consortium's for the sole purpose of driving the price wall up, and then cashing out once it reaches a predetermined price.
When you see cryptocurrency prices going up for no reason whatsoever, know that it’s a pump and dump in the making. If you want to partake, just make sure to get in early, enjoy the ride and cash out quickly. However, we don’t recommend investing in schemes like this at all.
There are communities that are solely dedicated to this. The go in and buy huge quantities of a certain cryptocurrency, watch the price artificially inflated and others get on board, then dump the coins after making a lot of money.
How To Protect Yourself From These Cryptocurrency Scams

There’s one simple thing to look for, and that is the use of cryptocurrency. Always lookout for the following when looking to invest in a cryptocurrency:
- An active community
- A development team dedicated to the project
- Transparency from the company
- Valid viable use case that solves actual problems
- History
Always research a cryptocurrency before investing in it. A simple search string like “[intended cryptocurrency] daily reddit” will be enough to show if they are legit or not. Also look for mentions in major news outlets, visible team leads with a track record of results in and/or outside the industry and backers.














